Call Me By My Name — in my dream world
You’re my uncle, sister, friend, mother, nephew or colleague. You want to message me, send me your photos and news, read my latest blog post, have a video call. Where do you go, online? You know my phone number, my email address, but just now you're not looking to call or email me.
Meet Me at the Club?
In the Dark Old Days you’d pull out your Big Tech membership cards: you might look for my updates in the Facepalm Club, try the Googol Club if it’s photos you’re sharing, or go to the Whatsitt Club to message me. But then can you recall whether I’m a fellow member in each of your clubs? And am I likely to be visiting that particular club (opening its app) today?
Comfortable though some of its members may be while eating, exercising, chatting together in their club, it’s a weak friendship that exists only there. Real friends call each other directly and meet up where we choose.
Back then, I used to maintain a membership of some of those clubs reluctantly, out of FOMO. When you called me to meet you in one of those silos, I wanted to make it easy for you, so I gritted my teeth and entered, detesting the feeling of being pushed into an environment built for advertising and surveillance and controlling what I am allowed to do. I never visited those places of my own volition.
Call Me by My Name
In my dream, you reach me online using my digital personal identifier. You know my email address is julian@foad.me.uk — well, that’s also my personal identifier. That’s all you need to know in order to reach me in other ways. No matter which app or service you are using, tell it to contact me at julian@foad.me.uk and the app will make an interactive data connection to my “digital self”, the computer system that represents me in the ether. (If you are familiar with technical protocols, think of something like a combination of DNS and WebFinger.)
Message me at julian@foad.me.uk from your favourite chat app without wondering what chat service provider I use; share your holiday photos to julian@foad.me.uk regardless whose data storage service I use on my end; read my blog at julian.foad.me.uk without some Big Tech watching and selling your activity data; make a video call to julian.foad.me.uk and only our own digital selves know about it.
The Restraining Order is Lifted
It’s as if in real life we had been living under a restraining order, we were previously limited to meeting each other only at a club or business premises, a restaurant or football match or cinema; and now the restriction is lifted and we are at last allowed to visit one another at our own homes. We no longer need those club membership cards.
Now that we are no longer required to meet only in clubs, we no longer alienate those of our friends who avoid or have difficulty going there because their other friends are banned or unwelcome. We can now associate freely with the friends who can’t in good conscience patronise those clubs: we no longer need force them to choose between our friendship and their conscience. Where we used to belong to a club that forbids our friends from bringing their young children in with them: we can meet at their own house instead. You are still free to join a club, of course, as am I, if we like spending time in there, but now I don’t have to join your club and you don't have to join my club in order for us to meet. Now we can communicate directly.
A Personal Identifier
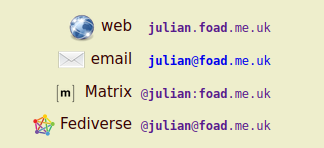
My main personal identifier is composed from my name julian at my family domain name foad.me.uk. We can use this identifier, spelled in slightly different ways, for multiple protocols:
julian.foad.me.uk— web, bluesky, indie-auth, ...julian@foad.me.uk— email, single-sign-on, ...@julian@foad.me.uk— xmpp/jabber, activitypub/fediverse (mastodon, peertube, pixelfed, lemmy, ...)@julian:foad.me.uk— matrix (IM, FUTO Circles, ThirdRoom, Commune, ...)
This is all the same “personal identifier”, in abstract, no matter that we punctuate it in different ways with “at” signs and dots and colons. (Most apps now use the x@y form.)
Multiple Personalities
This personal identifier is not the totality of my online identity. It reflects one aspect of myself. This one reflects my real name and I use it for serious real-life situations such as friends and authorities. I use other personal identifiers in other situations: my employer currently assigns me an identifier representing me in my job (mr.j.foad@my.employer), and I own a whole domain in which I can choose lots of pseudonyms that I use in playing games ({cat,dog,rat,hog,...}@pinball.wizard). From someone else’s point of view, my identifiers appear to be independent: they are not self-evidently associated with the same person. If I want to, I may reveal or prove the fact that two of my identifiers are associated.
DNS
The second part of the identifier is here assumed to be a DNS domain name. (Another time I might talk about my non-DNS identifiers, such as phone numbers and cryptographic keys.) DNS relies on registration with a central authority. I have an arrangement in place for keeping the family domain registered for the long term, so it’s not solely dependent on me renewing its registration: two or three family members share the legal responsibility for its upkeep, or a government or community organisation “underwrites” it for us.
Knowing that DNS has many associated problems — its inherentl centralisation, monetary cost, privacy and more — we certainly want to be looking ahead to using an identifier protocol that can support other systems as well. A promising one which I intend to study more is the identity component of 'atproto', an open protocol from the bluesky team.
Being Your Own Id
The key to using any such identifier, DNS or otherwise, as a basis for my own identity is that it should not be tied to and controlled by the service provider of my communication services. We must be free to change service provider while keeping our identity, bringing our own (independent) identifier away from the old service provider to the new service provider. Providers must support “Bring Your Own Id”. Our other open protocol providers, matrix and fediverse and so on, must catch up with what paid-for email providers have been offering forever. Let's see how that works.
Owning Our Own Email Address
A personal identifier in this context means one that we own personally, or at least independently of the service providers.
The domain name (after the “@”) shows who owns an email address. Some of us are using a Big Tech email address: somename@gmail.com, @hotmail.com, @msn.com, @outlook.com, etc. We are merely borrowing the use of any such address, for the limited purposes they want to allow. It is owned and controlled solely by the company that registers the domain name.
The key property of a personal identifier is that we retain the right and the ability to bring our own personal identifier to a new service provider and ask them to provide service to us using our own identifier, not one that they control.
If we use a Big Tech email address and are now wondering how we can use that as our personal identifier, how we can let our friends reach us in other ways through that same address, the plain truth is we can’t. (In theory the owning company could choose to let us use that borrowed address to identify and connect to other services, but that doesn’t match Big Tech’s business model.) That’s OK. We can work around the problem. First we need to get ourself a personally owned identifier, and start using it for everything else. Whenever we’re ready, and only once we're comfortable that's the right thing to do, then we can change our email over to our own address as well.
This article is (maybe) part of a series on how tech works in my dreams. I decided a dream is more likely to come true if I write it down. Then you might read it, and if we share the same dream, maybe together we might implement it.
Some of the names in this article are fictional. Some of the facts are fictional too, at the time of writing.
— julian@foad
Follow/Feedback/Contact: RSS feed · Fedi follow this blog: @julian@wrily.foad.me.uk · matrix me · Fedi follow me · email me · julian.foad.me.uk Donate: via Liberapay All posts © Julian Foad and licensed CC-BY-ND except quotes, translations, or where stated otherwise